Choosing a Safe and Secure Video Conferencing Solution
We walk you through what to look out for in terms of privacy and security when choosing a video conferencing solution.

To reduce the total cost of ownership, businesses will, in many cases, resort to outsourcing or relying on tools and services from third party vendors. And it makes sense, if you don’t have the time, budget or expertise in-house to build and manage a solution, why not let somebody who does have that expertise and who has spent years perfecting the technology take care of it for you?
It goes without saying that this applies to video call technology and vendors. You’re looking to hold video meetings or add real-time video communication into your platform, but have no idea where to start. Your first step is likely to see what video platforms and vendors already exist. It makes sense to leverage a third-party-operated scalable, robust and secure-enough video infrastructure rather than building it from scratch on your own.
While the benefit is clearly there, it does not come without a price. Both financially but also operationally. The long-term cost saving from choosing a ready-made solution is clear, both in terms of hard cash and work hours, but there’s still considerations to be made. With so many video conferencing platforms available, it can be difficult to compare and assess which solution is right for you and your business.
How do you know which one is the right fit? How will it play with your existing infrastructure? What are the criteria that matter to you the most during selection?
There are many factors to consider, and one which will heavily influence the decision for many organizations is security and privacy.
Choosing your video vendor from a privacy and security perspective
There are various considerations that can come into play here, but two of the most important are external security posture, and data storage and processing. Keep reading to find out what to look out for when comparing and assessing real-time video vendors.
1. External Security Posture
Industry renowned certifications such as ISO27001, audit reports such as SOC2 or a penetration test are key evidence, highlighting that a reputable, objective 3rd party has investigated whether the company has a good posture in place. Look to see if these are mentioned on the vendor's website (like on our security page or security portal).
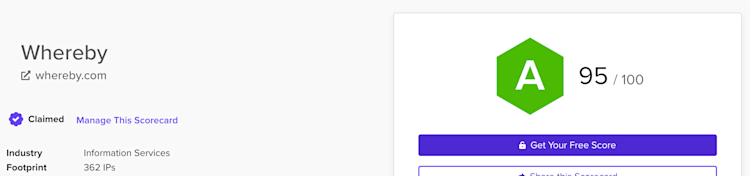
Another way to assess a company's security posture is to take a look at tools that gather open information about a company’s external security posture such as SecurityScorecard and other similar tools.
As of October 21st 2022*, Whereby scores very highly on SecurityScorecard, leading the embedded video space.
*These scores are subject to change given the very dynamic nature of infrastructure and security developments
You can see the scores for some other real-time video platforms below:
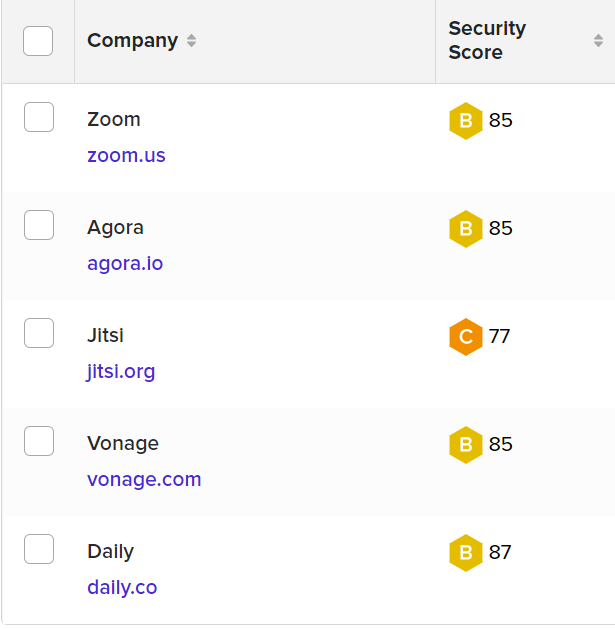
These scores are of course ever changing, so it’s important to check the most up-to-date information when you’re assessing a vendor. A company’s security posture is constantly changing and adapting alongside the development of its products, services and infrastructure.
2. Data Processing
A privacy policy and a terms of service should always be present on the website of any SaaS vendor, especially a real-time video solution. In an ideal world, the less data processed by a company, the better. However there will always be a fundamental need to process some data in order for the service to function.
Being able to respond to data subject requests in a timely and appropriate manner is an indicator that the 3rd party vendor knows what personal data is processed, where and can take action on it according to the data subject request.
Historic information on whether there have been any data breaches can also be a good indicator of poorly handled data. Given that data breaches have become the global norm rather than the exception, some feel it’s a matter of “when” not necessary “if” it will happen. If it did happen to the vendor you are considering, be sure to understand the specifics around it. Why did it happen? What was affected? How did the company respond?
A data breach might not necessarily be a show stopper if the vendor responded well to the incident, informed those affected, took the necessary actions in due time and learned from the incident, thus improving their posture as a result.
One last, but crucial aspect in processing of data is the transparency around it and the security controls used. The industry typically relies on questionnaires where security controls are described and questions are asked around them. Whereby has such a questionnaire publicly available as part of the Cloud Security Alliance STAR registry, reducing the hassle required to get these answers.
What can happen if you don’t consider these aspects?
There can be some tough consequences if you don’t take privacy and security posture into consideration when deciding on vendors. Some of the main issues could be:
Regulatory fines - GDPR is known for being used to hit companies with major fines for not being transparent enough and for not properly processing personal data.
A bad user experience - Security vulnerabilities can affect users and how they use the service, particularly from an availability standpoint (DDoS attacks, account takeovers or even having meetings disrupted).
Reputational damage - Being associated with a company that does not keep their security and privacy posture up to standards can also affect your company’s reputation. Customers may not be interested in who was to blame for a security incident specifically. When your company subcontracts another for certain services such as video calls, and that subcontracted company is breached, the blame will mostly fall on you in the public eye. Given that you were responsible for ensuring that the security of your contractors is adequate enough, customers will look to you for the blame and not the subcontracted company directly.
Overall, privacy and security should be top priority when choosing a real-time video vendor to integrate into your platform, website or app. At Whereby, we take this very seriously and are here to answer any questions you may have.


